CSRF
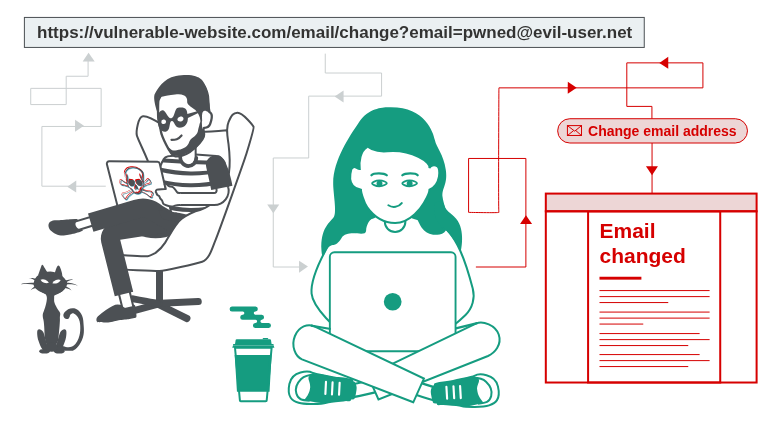
Cross-Site Request Forgery (CSRF) is an attack that forces an end user to execute unwanted actions on a web application in which they’re currently authenticated. With a little help of social engineering (such as sending a link via email or chat), an attacker may trick the users of a web application into executing actions of the attacker’s choosing. If the victim is a normal user, a successful CSRF attack can force the user to perform state changing requests like transferring funds, changing their email address, and so forth. If the victim is an administrative account, CSRF can compromise the entire web application.
For a CSRF attack to be possible, three key conditions must be in place:
- A relevant action. There is an action within the application that the attacker has a reason to induce. This might be a privileged action (such as modifying permissions for other users) or any action on user-specific data (such as changing the user's own password).
- Cookie-based session handling. Performing the action involves issuing one or more HTTP requests, and the application relies solely on session cookies to identify the user who has made the requests. There is no other mechanism in place for tracking sessions or validating user requests.
- No unpredictable request parameters. The requests that perform the action do not contain any parameters whose values the attacker cannot determine or guess. For example, when causing a user to change their password, the function is not vulnerable if an attacker needs to know the value of the existing password.
That last one, no unpredictable request parameters, is exactly why csrf tokens exist. They're random and unpredictable deliberately.
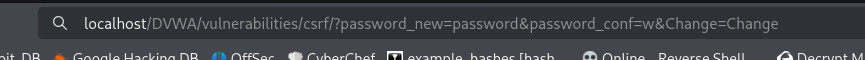
DVWA CSRF - Low
The task is to make the current user change their own password, without them knowing using CSRF.
At low level, we'll craft a link to achieve a certain action (in this case changing the current user's password) Then using some basic social engineering, have the target click the link or visit a certain page to trigger the action.
Essentially, a phishing email with this URL attached sent to a targeted user. Then used to log in as that user with the credentials we set.